Intro to Cybersecurity:
Learn to defend.
Think like security.
Build real skills fast.
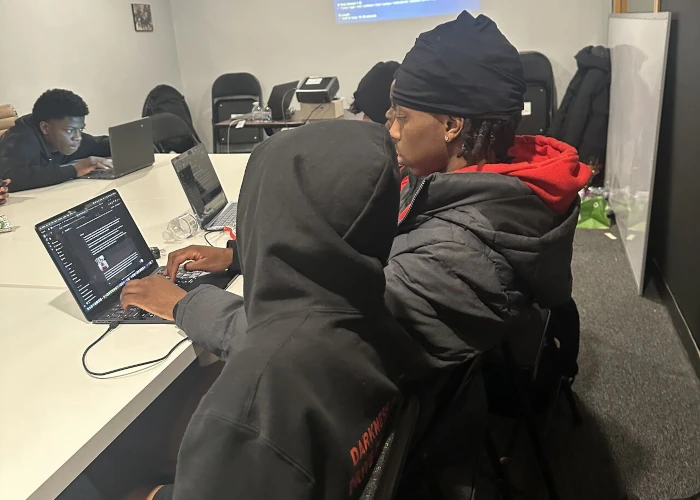
A hands-on, beginner-friendly program that
teaches the foundations of cybersecurity risk,
networks, threats, and real-world defense—so
you can protect yourself, contribute on day
one, and start building momentum toward
Security+ pathways.
Most people only think about cybersecurity after
something goes wrong an account gets hacked,
a device gets compromised, or a job requires
security knowledge they don’t have.
to evaluate risk through guided instruction, exercises, and hands-on practice.
What You’ll Learn
 |
Cybersecurity FoundationsThe cybersecurity industry, why security matters, common roles and certifications, and what success looks like |
 |
Risk ManagementHow businesses think about risk, why the “weakest link” matters, and how risk decisions get made |
 |
Network Security Basics & EssentialsHow networks work, where attackers exploit weaknesses, and core network security concepts |
 |
Linux Basics & EssentialsFoundational Linux concepts that show up constantly in security environments |
 |
Microsoft Basics & EssentialsSecurity fundamentals in Microsoft environments and what “enterprise security” looks like |
 |
Application Security
|
 |
Offensive Security ConceptsWhy offensive security exists, frameworks like MITRE ATT&CK / kill chain thinking, and how attackers operate |
 |
Threats & Threat ActorsTactics, techniques, and procedures (TTPs), plus notable breaches and what we learn from them |
 |
Core Topics ThroughoutBasic cryptography, malware, social engineering, incident response, plus legal and ethical considerations |
No overpromises. Just leverage you can actually use.

If you want a job path:
Cybersecurity knowledge strengthens
your eligibility for entry-level
tech roles and helps you stand out
when employers want security
awareness—especially as organizations
tighten defenses.

If you’re upgrading your skills for your current role:
You’ll understand the “why” behind
policies and tools—so you can
contribute more, communicate better,
and take on higher-value
responsibilities.

If you’re protecting yourself and your household:
You’ll understand what to watch
for, how breaches happen, and
how to reduce risk in a
practical way.
Proof the Market Is Active
Cybersecurity is not optional anymore—demand keeps rising as threats increase and organizations invest in defense.
Why this matters for you:
There are hundreds of thousands of cybersecurity-related job postings nationally each year, and Information Security
Analyst roles are projected to grow fast over the next decade. If you build the foundation now, you put yourself in
position for the next step.
Pricing &
Enrollment
Tuition: $5500
Total training time: 28 hours
Start date: [Start Date]
Enrollment deadline: [Date]
Urgency line: If you want in, apply now—don’t wait until the start date is around the corner.
Frequently Asked Questions
Do I need experience?
No. This course is designed for beginners.
What do I need technically?
A laptop/computer, reliable internet, and the ability to run a virtual machine environment.
Is this technical?
Yes—but it’s structured so you can learn the concepts and apply them without drowning.
Is it self-paced?
No. It’s live online with structure, deadlines, and feedback.
Step into cybersecurity with real skills
not just curiosity.
toward a real path, apply now.